About ArcForgeLabs
Why these tools exist.
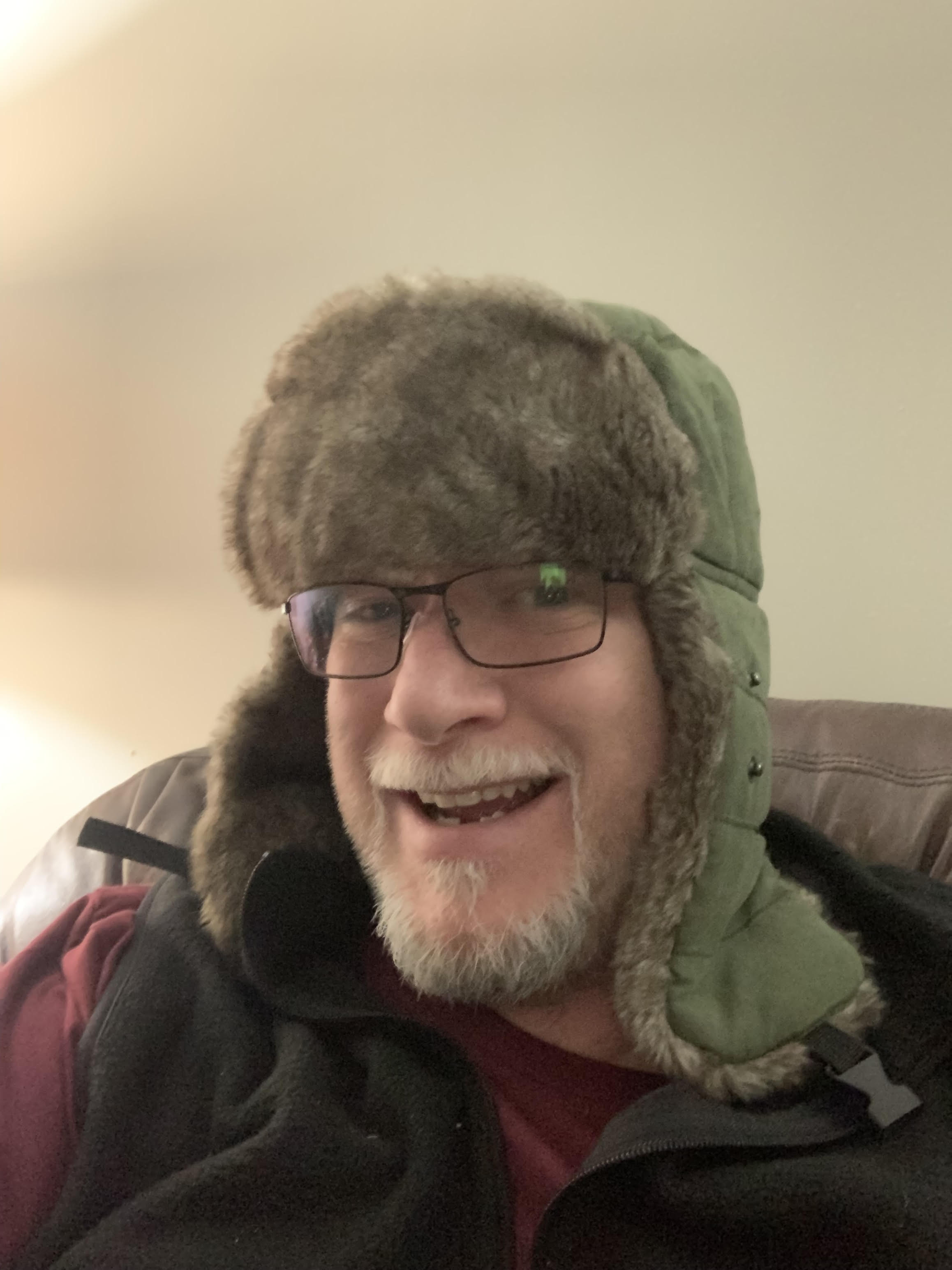
Patrick Donohue
IT Infrastructure & Cybersecurity — Spokane, WA
35+ years in IT infrastructure and cybersecurity, most recently in the financial sector. Author of API-ocalypse Now: Python’s Guide to Secure and Flexible Data Handling. Builder of tools that solve problems I’ve actually run into.
ArcForgeLabs exists because two categories of problem kept appearing across the production environments I’ve worked in.
The first: your domain is a public artifact. DNS records, email authentication policies, TLS certificates, HTTP headers, subdomains — all of it is queryable by anyone with a terminal. Attackers run exactly this reconnaissance before deciding whether to pursue a target.
The second: employees report suspicious emails all the time. No response, no feedback, no triage — which means the next person to receive the same phish has no better odds than the first.
Enterprise IT, financial sector infrastructure — the kind of work where configuration mistakes have real consequences and a phishing email reaching the wrong person isn’t theoretical. These tools automate that diagnostic work.
Neither tool will replace a full penetration test or a comprehensive security audit. What they will do is tell you whether the basics are covered before you spend money on something more elaborate.
How I build things
Every tool I build follows the same rule: answers, not dashboards. A finding that requires a security specialist to interpret is not useful to the person responsible for acting on it. “Your DMARC record is missing, here’s what that means for you” is more actionable than a risk score on a dial.
Results are deterministic and explainable. No black boxes, no model inference applied to something that doesn’t need it. Every finding has a source. Every score has a calculation. If you want to know why something flagged, the information is there.
And every tool is explicit about scope. Surface Sentinel reads only what is publicly visible — if it can see something, an attacker can too. Ephemeral Sentinel checks signals, it doesn’t guess. Trace Sentinel applies deterministic rules, not model inference. None overpromises. Overstating what a tool does is worse than understating it.
The tools
The advisory side
Tools show you the problem. Sometimes you need help solving it — without a consulting firm engagement, a statement of work, or advice filtered through a sales process.
I offer direct advisory for teams that found something and need to know what to do about it: remediation guidance, practical prioritization, honest answers. Decades of real-environment experience, not vendor certifications.